The 8 Cryptographic Hash Properties Essential for Blockchain Security

Imagine you are handing a sealed envelope to a stranger. You need absolute certainty that nobody opened it, read the contents, or swapped the paper inside before it reached its destination. In the physical world, we use wax seals or tamper-evident tape. In the digital world of blockchain, a decentralized, immutable ledger technology that records transactions across multiple computers, we rely on something far more robust: cryptographic hash functions.
These mathematical algorithms are the silent guardians of your Bitcoin wallet, the Ethereum smart contract, and every other distributed ledger system. They don't just store data; they prove that data hasn't been touched. But not all hash functions are created equal. For a blockchain to remain secure, transparent, and trustworthy, the underlying hash function must satisfy eight specific, non-negotiable properties. If even one of these fails, the entire chain collapses under the weight of fraud and manipulation.
The Core Definition: What Is a Cryptographic Hash?
At its simplest, a cryptographic hash function is a mathematical algorithm that converts input data of any size into a fixed-size string of characters. Think of it as a digital fingerprint. You can feed it a single letter, a whole novel, or a terabyte of video files, and it will always spit out a string of the exact same length. This output is called a "digest" or "hash value."
In blockchain contexts, this process is one-way. You can easily turn the book into the fingerprint, but you cannot turn the fingerprint back into the book. This irreversibility is what makes blockchains secure. The most famous example is SHA-256, Secure Hash Algorithm 256-bit, the standard cryptographic hash function used by Bitcoin. When you send Bitcoin, your transaction data is hashed using SHA-256. That hash becomes part of the block's identity. If someone tries to change the amount you sent, the hash changes completely, invalidating the block and alerting the network.
Property 1: Deterministic Behavior
The first requirement is simplicity itself: consistency. A cryptographic hash function must be deterministic. This means that if you input the exact same data twice, you must get the exact same hash output both times. No surprises, no randomness.
Why does this matter? Because blockchain is a distributed system. Thousands of nodes (computers) around the world verify transactions independently. If Node A in Wellington calculates a different hash than Node B in Tokyo for the same transaction, the network breaks. Consensus becomes impossible. Determinism ensures that every participant agrees on the state of the ledger without needing to trust each other. It is the foundation of shared truth.
Property 2: Preimage Resistance (One-Wayness)
This property is often described as "one-wayness." Given a hash output, it should be computationally infeasible to reverse-engineer the original input. If I give you the hash `e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855`, you should not be able to figure out that the input was an empty string.
In practical terms, this protects user privacy and data integrity. If blockchains were not preimage resistant, anyone could look at a public transaction hash and deduce the private keys or sensitive personal information embedded within it. Since brute-forcing a modern hash like SHA-256 would take longer than the age of the universe with current computing power, your data remains safe behind the mathematical curtain.
Property 3: Second Preimage Resistance
Closely related to preimage resistance, this property prevents a slightly different attack. Here, an attacker already has a valid message and its corresponding hash. The goal is to find a *different* message that produces the *same* hash.
If this were possible, an attacker could replace a legitimate contract or transaction with a fraudulent one while keeping the same hash signature. The network would accept the fake because the hash matches the expected value. Second preimage resistance ensures that once a piece of data is hashed, no alternative version can masquerade as the original. It locks the data in place.
Property 4: Collision Resistance
This is arguably the most critical property for blockchain security. Collision resistance means it is extremely difficult to find *any* two different inputs that produce the same hash output. Unlike second preimage resistance, where the attacker starts with one known input, here they can choose both inputs freely.
If collisions were easy to find, an attacker could create two different transactions-one honest and one malicious-that share the same hash. They could broadcast the honest one to get it confirmed, then swap it for the malicious one later. The network would see the same hash and assume nothing changed. Modern algorithms like SHA-3, the latest generation of Secure Hash Algorithms designed to resist quantum attacks and BLAKE2 are engineered to make finding such collisions mathematically improbable.
Property 5: The Avalanche Effect
You might think that changing one bit in a large file would result in a small change in the hash. That is exactly what we do not want. The avalanche effect dictates that a tiny change in the input-like flipping a single zero to a one-should result in a drastically different hash output. Ideally, about 50% of the bits in the output should change.
This unpredictability is vital for mining and verification. If hashes were predictable based on minor edits, attackers could tweak transaction data incrementally to find favorable outcomes. The avalanche effect ensures that the relationship between input and output appears random, even though it is deterministic. It destroys any pattern an attacker might try to exploit.
Property 6: Puzzle Friendliness
This property is unique to blockchain consensus mechanisms, specifically Proof-of-Work (PoW). Puzzle friendliness means that if you know part of the input, you cannot predict or calculate the remaining parts needed to achieve a specific hash target.
In Bitcoin mining, miners race to find a nonce (a number) that, when combined with the block data, produces a hash below a certain difficulty threshold. If the hash function weren't puzzle-friendly, a miner could look at the first half of the block data and deduce what the second half needs to be. Instead, they must guess blindly. This ensures that mining is a fair lottery based on computational power, not clever mathematical shortcuts.
Property 7: Fixed-Length Mapping
Regardless of whether you hash a single word or an entire library, the output must always be the same length. SHA-256 always outputs 256 bits. This fixed-length mapping simplifies storage, processing, and comparison.
Without this, the blockchain structure would become chaotic. Blocks would vary wildly in size depending on the transaction volume, making synchronization inefficient. Fixed lengths allow nodes to allocate memory precisely and verify data quickly. It also enables efficient data structures like Merkle Trees, which we will discuss next.
Property 8: Large Output Space
The final property relates to probability. The hash function must generate outputs from a massive space of possible values. For SHA-256, there are $2^{256}$ possible hashes. This number is so large that it exceeds the number of atoms in the observable universe.
A large output space minimizes the risk of accidental collisions. Even if billions of transactions occur daily, the statistical likelihood of two unrelated transactions sharing a hash is negligible. It provides a buffer against brute-force attacks, ensuring that the only way to break the system is through sheer luck, which is effectively impossible.
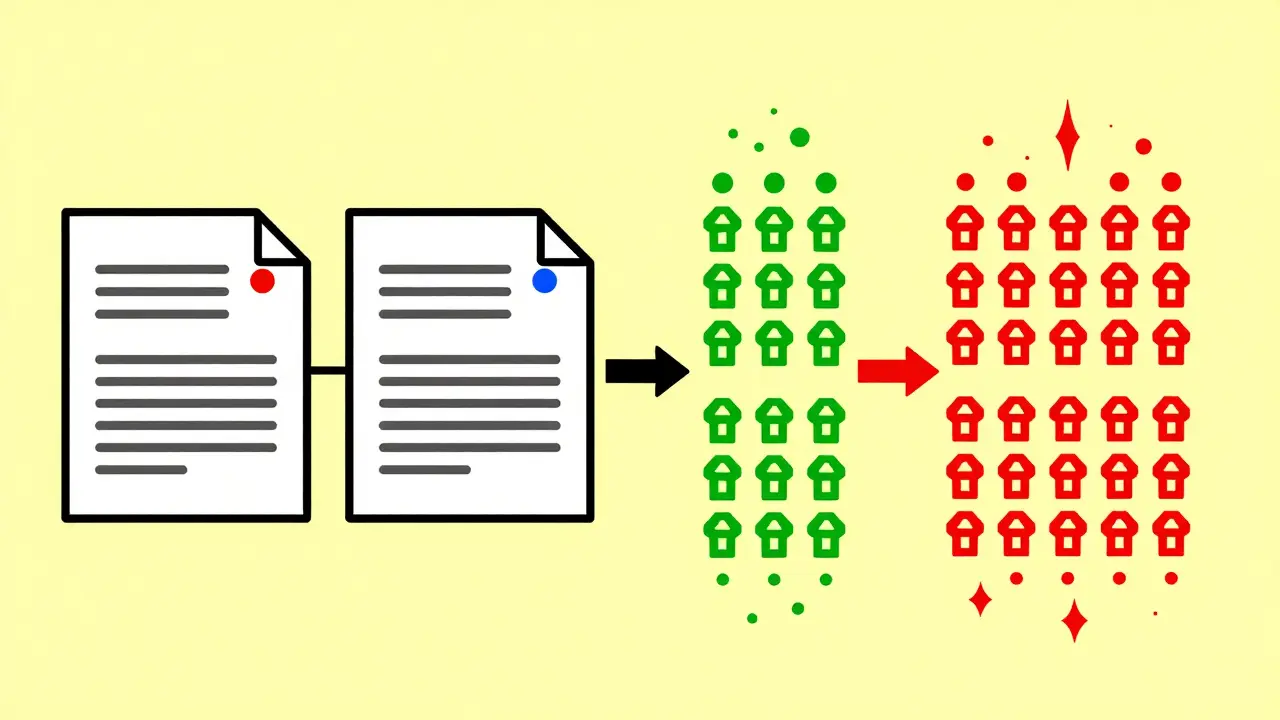
How These Properties Build Trust: Merkle Trees
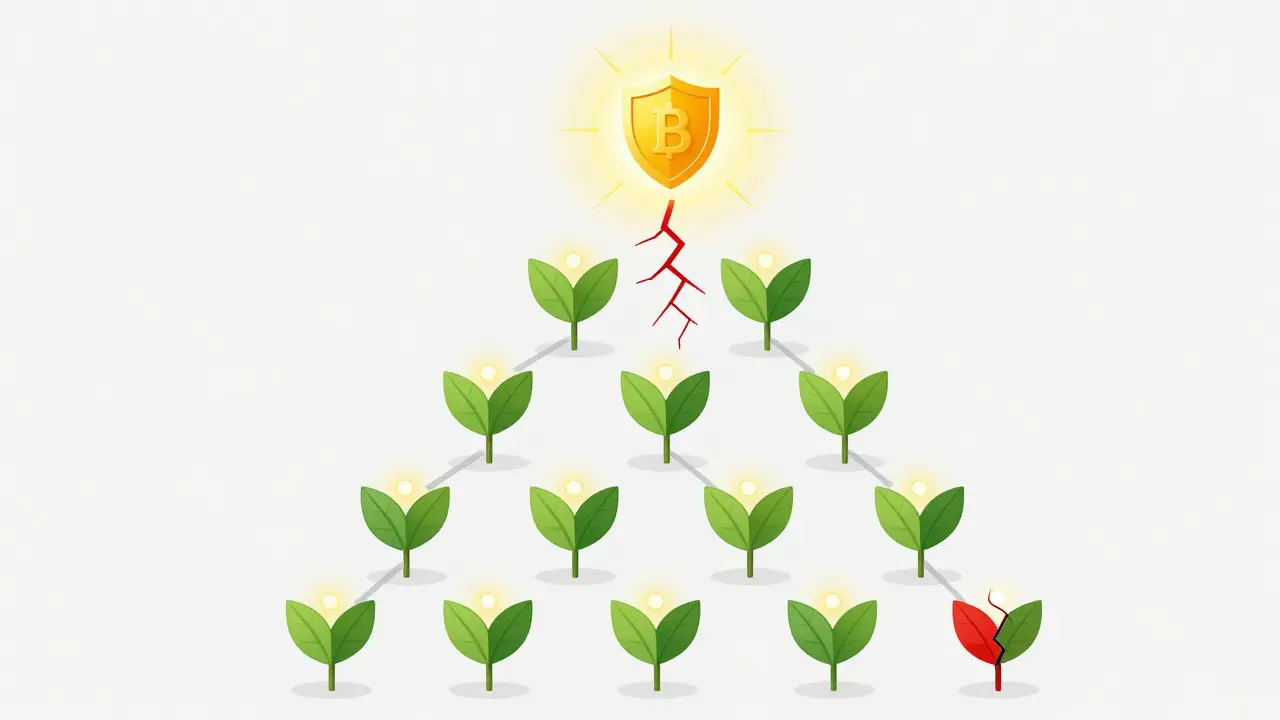
To see these properties in action, consider the Merkle Tree, a binary tree structure used in blockchains to efficiently verify large sets of data. Every transaction in a block is hashed. Those hashes are paired and hashed again, continuing up to a single root hash, known as the Merkle Root.
Because of the avalanche effect and collision resistance, if a hacker alters one transaction deep in the tree, the hash of that leaf changes. This change ripples up, altering every parent node until the Merkle Root itself changes. The network instantly sees a mismatch between the recorded root and the calculated root. The block is rejected. This efficiency allows lightweight wallets to verify millions of transactions without downloading the entire blockchain.
| Algorithm | Output Size | Primary Use Case | Key Strength |
|---|---|---|---|
| SHA-256 | 256 bits | Bitcoin, Ethereum (legacy) | Highly standardized, proven security |
| SHA-3 | Variable (up to 512) | Ethereum (post-Merge), newer chains | Quantum-resistant design |
| BLAKE2 | Variable | Zcash, Monero | Speed and efficiency |
| Scrypt | Variable | Litecoin, Dogecoin | Memory-hard, resists ASICs |
The Quantum Threat and Future Resilience
As we move toward 2026, the rise of quantum computing poses a theoretical threat to traditional cryptography. However, hash functions are relatively resilient. While Shor's algorithm threatens RSA encryption, Grover's algorithm only offers a quadratic speedup for searching hash spaces. This means that to maintain security, we simply need to double the hash length. Moving from SHA-256 to SHA-512 would neutralize most quantum threats.
Algorithms like SHA-3 are already designed with this in mind. Their sponge construction differs fundamentally from older designs, providing an extra layer of defense against unknown cryptanalytic breakthroughs. For now, the eight properties listed above remain the gold standard, ensuring that blockchains continue to operate as trustless, secure systems.
What happens if a hash function loses collision resistance?
If collision resistance fails, an attacker can create two different inputs that produce the same hash. In a blockchain, this could allow them to substitute a valid transaction with a fraudulent one while maintaining the same block signature. This would break the immutability of the ledger, leading to double-spending and loss of trust in the network.
Why is the avalanche effect important for blockchain mining?
The avalanche effect ensures that small changes in input data result in vastly different hash outputs. For mining, this means miners cannot predict how slight adjustments to their nonce will affect the final hash. It forces them to perform brute-force guesses, ensuring that mining is a fair competition based on computational power rather than mathematical insight.
Is SHA-256 still secure in 2026?
Yes, SHA-256 remains highly secure. While quantum computing advances pose theoretical risks, current quantum capabilities are not sufficient to break SHA-256. Furthermore, the blockchain community is actively monitoring these developments, and migration paths to post-quantum algorithms like SHA-3 are well-established if necessary.
How do Merkle Trees use hash properties?
Merkle Trees rely on deterministic hashing and the avalanche effect. Each leaf node is a hash of a transaction. Parent nodes are hashes of their children. If any transaction changes, its hash changes dramatically (avalanche effect), which propagates up to the root. This allows the network to verify the integrity of thousands of transactions by checking only one root hash.
What is the difference between preimage resistance and collision resistance?
Preimage resistance means you cannot reverse a hash to find the original input. Collision resistance means you cannot find two different inputs that produce the same hash. Preimage resistance protects privacy and secrecy, while collision resistance protects against forgery and substitution attacks.
