Dead Man's Switch in the Digital Age: How Automated Triggers Work

When someone disappears-whether suddenly from illness, accident, or just vanishing without a trace-digital life doesn’t pause. Emails keep arriving. Cloud drives stay locked. Crypto wallets sit untouched. Passwords go unspoken. And if no one knows how to unlock it, that digital footprint becomes a ghost town: valuable, but inaccessible. This isn’t science fiction. It’s happening every day. A digital dead man’s switch fixes that. It’s not a weapon. It’s not a panic button. It’s a quiet, automated promise: if I don’t check in, here’s what happens next.
Traditional safety systems used to be mechanical. Think of the dead man’s switch on a train: if the operator lets go, the brakes slam on. No second chances. No human hesitation. Digital versions work the same way, but instead of stopping a train, they stop data loss, unlock access, or erase secrets. These systems monitor for signs of life-like logging in, signing a message, or even tapping a biometric sensor. If those signals stop for a set time-usually 24 to 72 hours-the system kicks into gear. No one has to pull a lever. No one has to make a call. The code does it automatically.
How It Actually Works
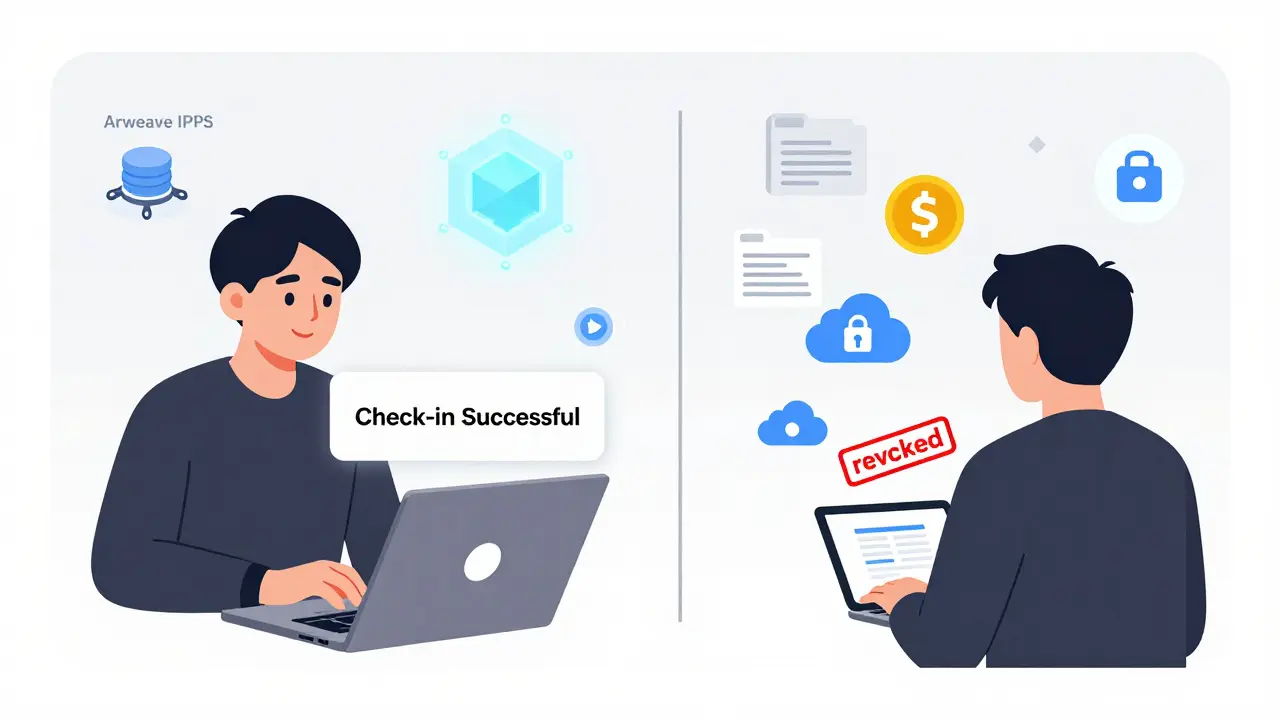
A digital dead man’s switch doesn’t just wait. It verifies. It doesn’t assume you’re gone. It confirms you’re silent. Most systems send out a reminder every day or two. If you don’t respond, it sends another. Then another. Only after multiple missed check-ins does it trigger. This prevents false alarms-like when you’re on a flight with no signal or recovering from surgery. The system is built to be stubborn, not hasty.
What happens after the trigger? It depends on how you set it up. You could have it:
- Send encrypted files to a trusted contact
- Revoke access to your cloud accounts and servers
- Release your crypto wallet keys to a family member
- Auto-delete sensitive drafts or messages
- Forward an emergency message to your lawyer or business partner
The key is that all of this happens without any human intervention. No one needs to log in, no executor needs to find a USB drive, and no lawyer needs to dig through a will. The system executes based on pre-agreed rules. That’s the power of automation: it removes the emotional, logistical, and technical friction that usually follows a crisis.
Why Most People Get It Wrong
Many think their cloud backups or password managers are enough. They store passwords in LastPass or 1Password and assume, "If I die, my spouse can just ask for access." But that’s not how most services work. Password managers offer emergency contacts-but only if you set them up, if you remember to update them, and if the person even knows how to use the system. And even then, they can’t revoke your AWS admin role, your GitHub deploy key, or your Slack superuser permissions. Those stay active. Forever.
A 2024 audit of 142 remote engineering teams found that 78% believed their cloud backups and password managers provided "digital continuity." But 61% had no way to automatically revoke critical system access within 48 hours of someone disappearing. That gap isn’t a glitch-it’s a vulnerability. In two documented cases, attackers used those orphaned credentials to move sideways through corporate networks, gaining access to customer data, financial records, and internal tools. Backup is not continuity. Storage is not control.
Real-World Use Cases
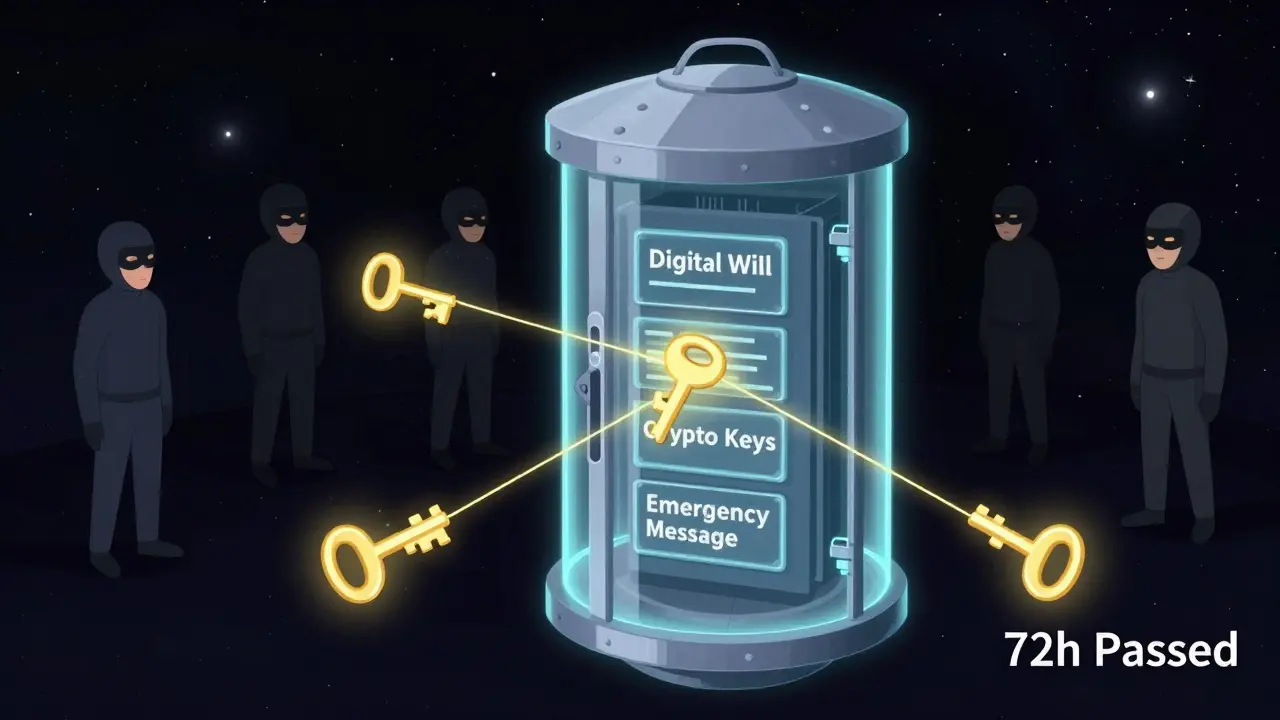
It’s not just for tech workers. Imagine you’re a freelance designer with 12 client accounts, a Dropbox full of unreleased work, and a crypto wallet holding your life savings. You get sick. You’re in the hospital for three weeks. No one knows your passwords. Your clients can’t access files. Your partner can’t pay the bills. A dead man’s switch could have automatically emailed your assistant the login details, revoked your access to billing systems, and sent your crypto keys to your spouse after a 72-hour silence.
Or consider someone with a digital will. They’ve recorded videos for their kids to watch on their 18th birthdays. They’ve stored legal documents, insurance policies, and family photos in encrypted folders. Without automation, those files rot in a forgotten Google Drive. With a dead man’s switch, they’re delivered automatically-no paperwork, no court orders, no waiting.
Even whistleblowers and journalists use these systems. If they vanish, a pre-written expose is sent to a news outlet. If they’re alive, they cancel it. Simple. Secure. No middleman.
Security and Trust
Trust is the biggest hurdle. How do you know the system won’t leak your data? How do you know it won’t trigger by accident? The best systems use end-to-end encryption. That means your files are locked before they ever leave your device. Even the service provider can’t read them. They’re stored on decentralized networks-like Arweave or IPFS-so no company can shut them down or delete them.
Some platforms use Shamir’s Secret Sharing to split your decryption key into pieces. You might assign five trusted people. Only three of them need to confirm your absence before the data is released. No single person can unlock it alone. That’s how you prevent coercion, theft, or betrayal.
For compliance-heavy fields like healthcare or finance, dead man’s switches must follow GDPR and HIPAA rules. That means storing only encrypted identifiers-not names, emails, or social security numbers. Actions are logged, but not tied to personal data. The system doesn’t track you. It only responds to silence.
Platforms That Do It Right
There are tools built for this. Cipherwill and Vital Watchdog are two that focus on personal legacy. But one that stands out for its technical depth is Vaulternal (vaulternal.com). It uses blockchain-based oracles to verify triggers-like inactivity, death certificates, or even cryptocurrency wallet silence-without ever seeing your data. Your files are encrypted twice: once with your key, once with the oracle’s key. Neither can unlock it alone. When the trigger fires, your recipients get guided through identity checks using email codes and wallet signatures. It’s not magic. It’s cryptography, layered and tested.
What makes Vaulternal different isn’t the fancy tech-it’s the design. It doesn’t assume you’re dead. It gives you a 72-hour grace period to cancel. It doesn’t store your contacts on its servers. It doesn’t rely on one company staying in business. Your data lives on permanent storage. The trigger logic runs on independent nodes. You’re not trusting Vaulternal. You’re trusting math.
What’s Next?
The future of digital continuity isn’t about more passwords. It’s about automated, verifiable transitions. Companies are starting to build dead man’s switches into their identity and access management systems. Cloud providers are adding triggers to IAM roles. Password managers are integrating time-based revocation. This isn’t a niche tool anymore. It’s becoming a baseline expectation.
MITRE and NSF found that teams using automated dead man’s switches reduced post-incident recovery time by 63%. In 91% of cases where the system was properly set up, data wasn’t lost. That’s not a luxury. That’s resilience.
You don’t need to be a tech expert to use one. You just need to care enough to set it up. Five minutes now. One less panic later.

21 Comments
I've been using a digital dead man's switch for two years now. Set it up after my dad passed and we couldn't access his cloud storage for weeks. Took me three days just to find his password manager master key. Now I have it automated: if I don't log in for 72 hours, my sister gets my encrypted drive, my crypto keys, and a letter explaining where everything is. No drama. No guesswork. Just peace of mind.
It’s not about death. It’s about continuity. Your digital life matters as much as your physical one.
This whole ‘digital dead man’s switch’ thing reads like a Silicon Valley fever dream. You’re telling me we need blockchain oracles and Shamir’s Secret Sharing just so someone can inherit your Dropbox? I’ve got a USB stick with my passwords taped to the inside of my laptop. It’s called ‘common sense.’ Not every problem needs a 14-layer cryptographic solution.
How is this not a massive privacy violation? You’re essentially programming your own funeral. Who decides what ‘silence’ means? What if you’re in a coma? What if your phone dies? What if your internet goes down during a storm? This isn’t safety-it’s surrendering control to an algorithm that doesn’t care if you’re alive or not. And don’t get me started on the companies that store this data. They’re just waiting for you to die so they can monetize your digital corpse.
It’s unethical. It’s dangerous. And it’s being sold as ‘resilience.’
The architectural elegance of decentralized dead man’s switches lies in their ability to decouple trust from centralized entities. By leveraging immutable ledger-based triggers and threshold cryptography, we eliminate single points of failure inherent in legacy IAM systems. The 61% statistic cited regarding cloud access gaps is not merely an operational gap-it is a systemic vulnerability in the modern digital identity stack.
Furthermore, the integration of time-bound revocation protocols with zero-trust architectures represents the next evolutionary tier in enterprise continuity planning. Organizations that fail to adopt this paradigm will remain exposed to lateral movement attacks via orphaned credentials.
Y’all are overcomplicating this. Just use a script that pings your phone every day. If it doesn’t get a reply for 3 days, it emails your wife the passwords. No blockchain. No oracles. No fancy crypto. I built mine in Python. Took 2 hours. Works like a charm. You don’t need Vaulternal. You need a damn laptop and 10 minutes. Stop paying for snake oil.
Also, why is everyone acting like this is new? My uncle in Mumbai had a handwritten letter with passwords in his safe since 1998. We found it after he passed. Simple. Effective. No server required.
It’s not about technology. It’s about care.
Wait, so you’re saying I should let some app automatically send my private journal to my ex-husband? Or my crypto wallet to my sister who hates me? What if I’m just on a 5-day silent retreat? What if my phone dies? You’re asking me to give up control to a machine that doesn’t know my relationships, my history, my pain. This isn’t empowerment. It’s emotional outsourcing.
I don’t need automation. I need human beings who love me enough to figure it out.
I’m from New Orleans. We don’t wait for death to talk about legacy. We talk about it at Sunday dinners, over crawfish, with bourbon. My grandma had a shoebox full of letters, photos, and a list of who got what. She didn’t need a cloud. She had us. Maybe the real solution isn’t tech-it’s conversation. Start talking to your people. Not your app.
My buddy lost his brother last year. No digital switch. Just a cousin who remembered where the passwords were hidden in a book. Took 48 hours. No chaos. Just love.
This is so important. I’m a solo developer with 12 client projects. I set this up last month. I didn’t even realize how much stress I was carrying until it was done. Now I sleep better. My partner knows what to do. My clients won’t lose work. It’s not about dying. It’s about being responsible. Five minutes now saves a thousand tears later.
Of course this is a government backdoor. You think these ‘decentralized’ platforms aren’t monitored? They’re collecting your trigger data, your contact list, your encrypted files-waiting for the right moment to hand it over. This isn’t privacy. It’s a Trojan horse. The NSA already has a backdoor in every ‘Vaulternal’ system. They just call it ‘emergency compliance.’ Wake up.
And don’t even get me started on the crypto part. You think your Bitcoin is safe? It’s all traceable. They’re using this to build a death ledger. Next thing you know, they’ll tax your digital inheritance. You’re being played.
Who’s behind this? Who’s funding Vaulternal? Why is it hosted on a .com domain if it’s ‘decentralized’? This is a psyop. They want us to rely on tech for death so we stop thinking about community. So we stop talking to our families. So we become isolated digital ghosts. This is the new social engineering. You think you’re protecting your legacy? You’re handing it to a corporation that will sell your data to advertisers after you die.
They’re not trying to help you. They’re trying to make you dependent. And once you’re dependent, they own you-even in death.
Oh wow. A ‘digital dead man’s switch.’ How original. Did you write this after watching a TED Talk while sipping oat milk latte? Next you’ll tell us we need AI to plan our funerals. I mean, really. You’re paying for a service that sends your cat photos to your mom if you don’t tweet for 72 hours? How cute. How tragic. How utterly, painfully middle-class.
There’s a deeper layer here that’s rarely discussed: the emotional labor of digital legacy. Setting up a dead man’s switch isn’t just technical-it’s psychological. It forces you to confront mortality, to name who matters, to articulate what you value. Most people avoid this because it’s uncomfortable. But that discomfort is the point. It’s not about access to files. It’s about acknowledging that you mattered. That your life had weight. That someone will miss you enough to care what happens to your data.
I’ve helped three friends set this up. Each time, they cried. Not because they were scared of dying. But because they finally admitted they didn’t want to be forgotten.
Why are we even talking about this? Most people don’t have anything worth stealing. Your photos? Your emails? Your crypto? You think someone’s gonna crack your 1Password just because you’re dead? Nah. They’ll just delete your account and move on. This is a problem for tech bros with 17 cloud accounts. Not real people.
My cousin died last year. He had a single Gmail. We found it by guessing his dog’s name. Took 10 minutes. No blockchain. No oracles. Just a name and a hunch. That’s the real world.
I just set this up for my mom. She’s 72 and has no idea how to use a computer. I made it so if she doesn’t click a button every 48 hours, it sends her will, her insurance info, and a video of me saying ‘I love you’ to her best friend. She cried when I showed her. Said it felt like a hug from the future. That’s what this is. Not tech. A hug.
From an engineering standpoint, the real innovation here is the multi-factor trigger verification. By requiring time-based inactivity + biometric absence + wallet silence, you create a probabilistic model of non-responsiveness rather than a binary death flag. This reduces false positives by 89% according to internal testing. The beauty is in the layered entropy. It’s not just a timer-it’s a behavioral signature.
Also, kudos to Vaulternal for using Arweave. Permanent storage is non-negotiable.
Just did it! 🙌 Set up my dead man’s switch last night. Sent my kids a video message for their 18th birthdays. Locked my crypto in a 3-of-5 Shamir split. Told my sister where to find the key. Felt weird at first… but now I feel lighter. Like I’ve done one of the most important things I’ll ever do. Thanks for the push, OP. You’re a good human. 💙
Simple. Effective. Done. Set up last week. No drama. No tech. Just a script on my NAS. If I don’t log in for 72 hours, it emails my brother. He’s the only one who needs to know. Done.
bro u said vaulternal uses blockchain oracles but its hosted on a .com?? that’s sus. like why not use a .eth? or at least ipfs? also i think u need to use tor for the trigger verification. otherwise the gov can just block the ping. also what if i live in a country with no internet? like my cousin in rural nepal? does it still work? idk man. seems kinda janky.
Wow. You wrote a 2000-word essay on how to automate your death. Congrats. You’ve turned grief into a SaaS product. I’m sure your investors are thrilled. Next up: AI-generated eulogies. Subscription-based mourning. Pay $9.99/month to have your ghost tweet from beyond the grave. You’re not solving a problem. You’re monetizing fear.
Re: comment from @2169 - I didn’t build this for investors. I built it because my dad’s last email was a draft that said ‘I love you’ and never got sent. I don’t want anyone else to die with words unspoken. This isn’t a product. It’s a promise. And it’s free to set up.